はじめに
インダストリ4.0の中心にあるのは、ファクトリ・オートメーション(FA)です。そのため、インダストリ4.0の実現を目指す上ではロボットの存在が重要になります。つまり、組み立て作業などを担うロボットや、自律走行搬送ロボット(AMR:Autonomous Mobile Robot)、協働ロボット(コボット)など、産業用のロボット全般が重要な役割を担うということです。実際、現在のロボットはよりスマートで協調的なものになっています。しかも、人間の介入の有無にかかわらず複雑な作業をこなせるようになりつつあります。そのようにしてロボットの利用が拡大した結果、オートメーションのレベルは大きく向上しました。それに伴い、ロボットを制御するシステム(ロボット制御システム)の安全性とセキュリティの強化も強く求められるようになりました。
当初、ロボットは主に工場の製造フロアで使用されるものでした。それが現在では、医療、軍事、物流、農業といった様々な分野で活用されるようになっています。安全性とセキュリティは、10年ほど前と比べてはるかに重視されるようになりました。事故を完全に防止するのは難しいでしょうが、悪意ある攻撃は阻止できるようにしなければなりません。悪意を持った人にロボットが乗っ取られ、自由に制御されるようなことがあれば致命的です。それにより、経済的/財政的な面で深刻な事態に陥る可能性もあります。
ロボット制御システムが抱えるセキュリティ上のリスク
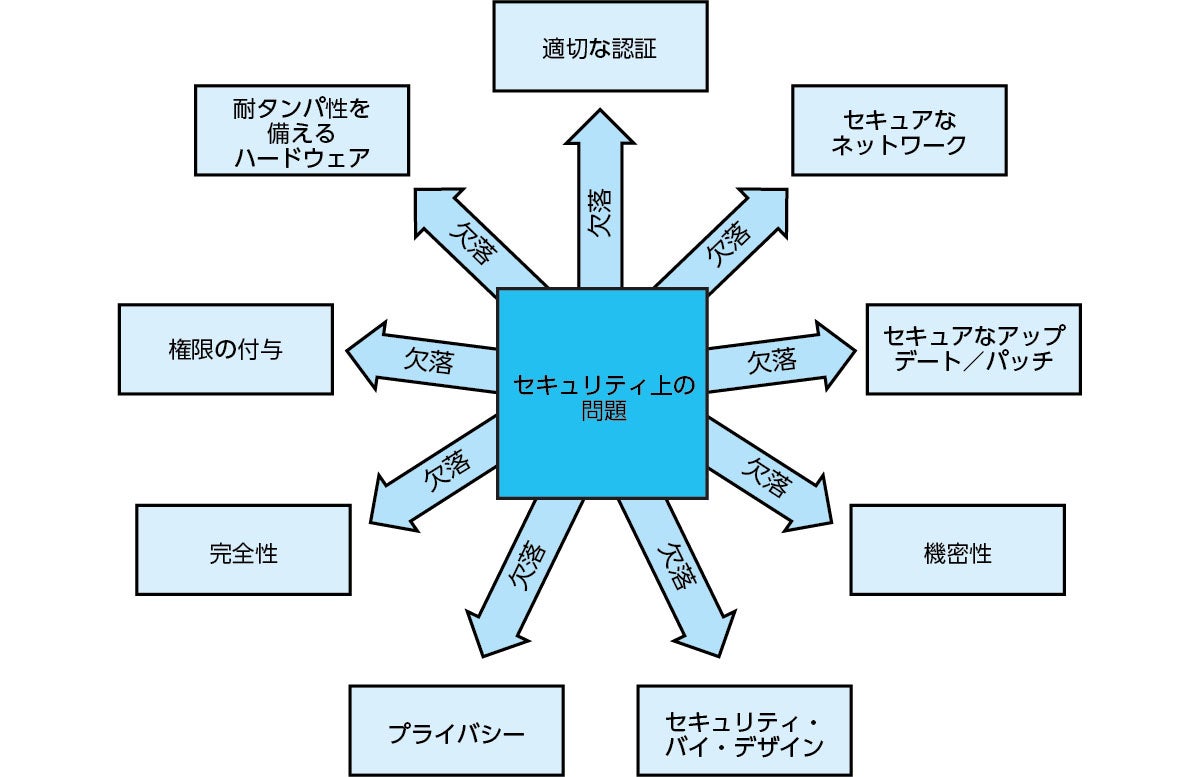
まずは図1をご覧ください。これは、ロボット制御システムが抱えるセキュリティ上のリスクについてまとめたものです。これらの要因により、ロボット制御システムは悪意ある攻撃にさらされる可能性があります1。
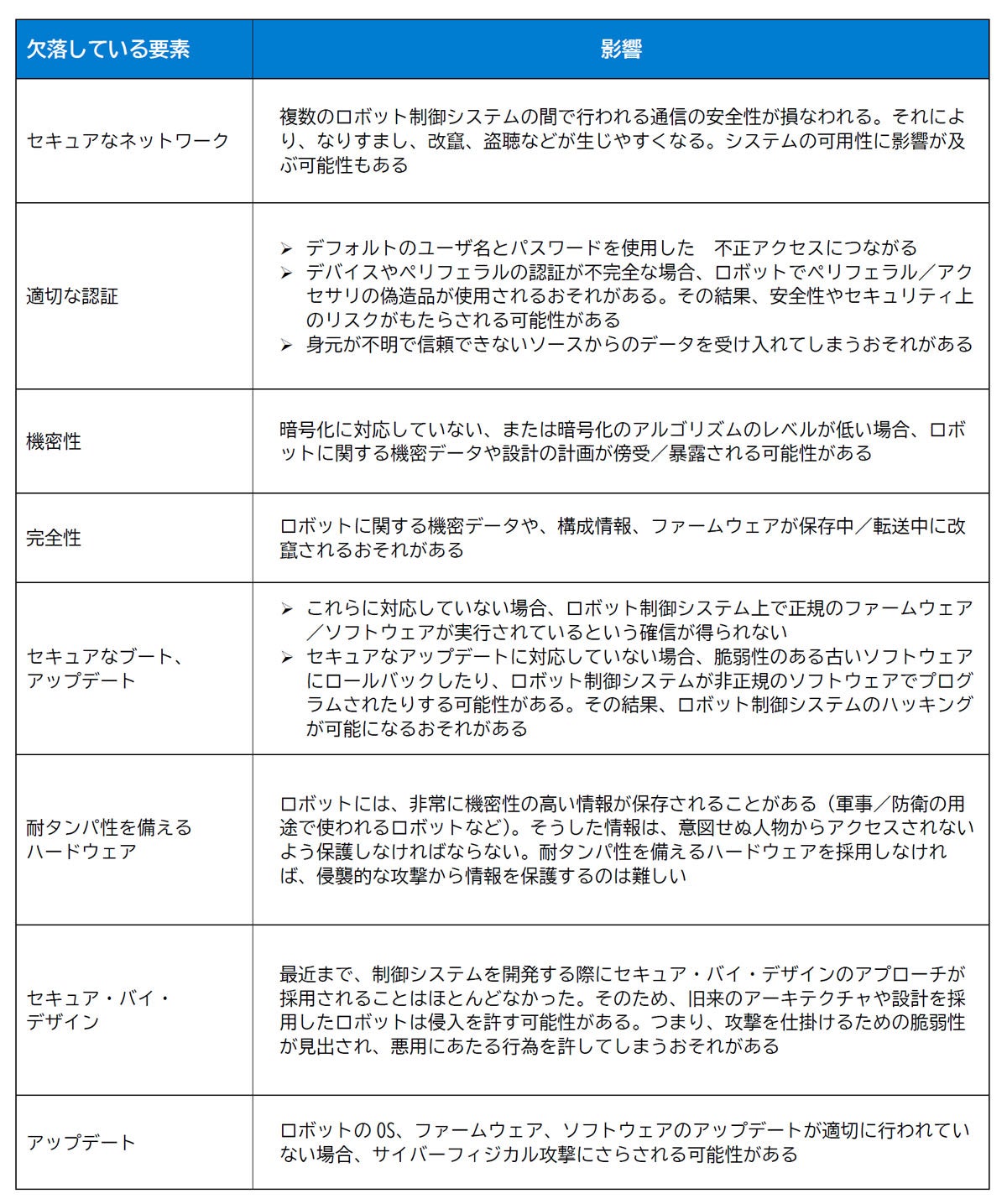
続いて、表1をご覧ください。これはいくつかの懸念事項の概要を示したものです。
産業/ロボット向けの法令、サイバー・レジリエンスと安全対策の強化を後押し
サイバーセキュリティを取り巻く状況は急速に変化しています。産業分野やロボットの分野を対象とした規制や法令が増えていることも、そうした変化の1つです。現在では、サイバーセキュリティを対象とした法律も少なくありません。代表的なものとしては、EUのサイバーセキュリティ法(EU Cybersecurity Act)やサイバー・レジリエンス法(EU Cyber Resilience Act)、米国の重要インフラ向けサイバー・インシデント報告法(U.S. Cyber Incident Reporting for Critical Infrastructures Act)が挙げられます。中国やインドでも新たな規制や法令が誕生しています。米国立標準技術研究所(NIST:National Institute of Standards and Technology)のOTセキュリティ・ガイド(Guide to Operational Technology(OT) Security)やIEC 62443のような規格は、技術企業にとっての指針になります。セキュア・バイ・デザインのアプローチを採用すれば、サイバー攻撃に対してレジリエントな制御システムを開発することができます。
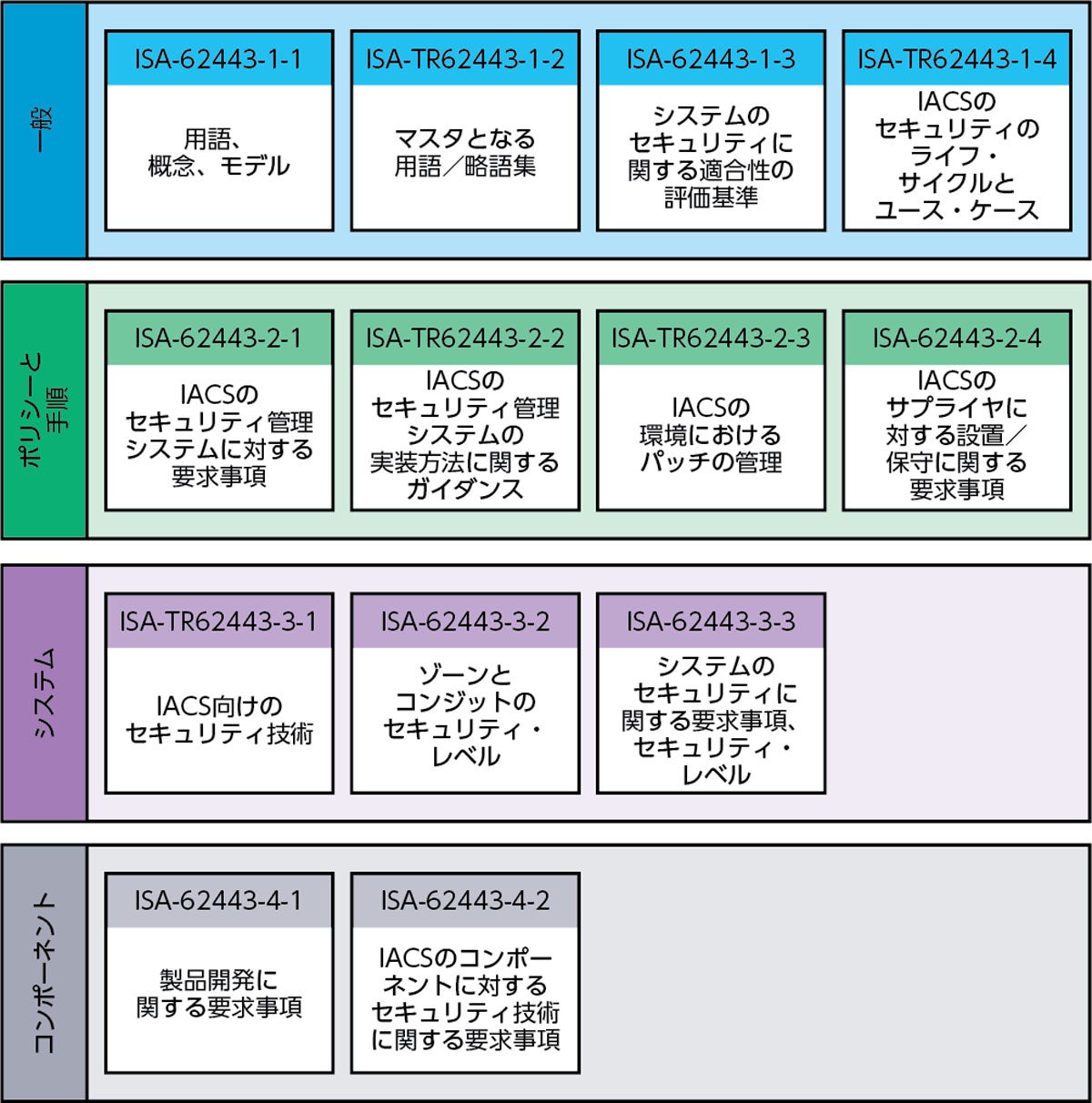
IEC 62443が定めるIACSの要件
IEC 62443は、IACS(Industrial Automation and Control Systems)のセキュリティに関する規格です2。産業用オートメーションの分野では、制御システムを開発する際の指針として広く採用されています。また、多くの規制においても、この規格に準拠することが推奨されています。つまり、その重要性は明らかだと言えるでしょう。実際、この規格に関連する規制に準拠すれば、制御システムが抱える潜在的なサイバーセキュリティのリスクを軽減することが可能になります。また、制御システムにおけるセキュリティ・ギャップに対処し、重要なアセットを保護することができます。IEC 62443に準拠すれば、多くのメリットを享受できるということです(図2)。
IEC 62443では、プロセスや手順について多くの事柄を規定しています。ただ、IEC 62443-4-1とIEC 62443-4-2では、コンポーネントのセキュリティに関する規定に重点が置かれています。IEC 62443-4-2では、コンポーネントを次のように分類しています。すなわち、ソフトウェア・アプリケーション、ホスト・デバイス、組み込みデバイス、ネットワーク・デバイスの4種です。この規格では、各種のコンポーネントに対する要求事項(CR:Component Requirement)と強化要求事項(RE:Requirement Enhancement)に基づいて機能のセキュリティ・レベル(SL:Security Level)を定めています。SL1からSL4までの4つのレベル(SL)のうち、SL3とSL4はハードウェア・ベースのセキュリティを必要とします。
ロボット向けセキュリティ・システムの開発に必要な機能と技術
セキュアなロボット制御システムを構築するには、図1と表1に示したリスクに対処する必要があります。技術的な面で必要な機能や技術としては、以下のようなものが挙げられます。
- セキュアな認証:デバイス/コンポーネントのIDを確認するためにセキュア認証用ICを採用する
- セキュアなコプロセッサ:セキュアなストレージと暗号化の処理に対応するための専用ハードウェアを活用する
- セキュアな通信:データ交換に対する保護を実現するために、暗号化用のプロトコルを実装する
- アクセス制御:システムに対する不正なアクセスを制限するために、権限をきめ細かく設定する
- 物理的なセキュリティ対策:物理的な改竄を防ぐための対策を導入する
セキュア認証用ICやコプロセッサICなどはターンキーのソリューションとして設計されています。それらは上記の要件を満たすことを目的としたものであり、実装が容易でコスト効率に優れています。このような専用ICの機能は、ホスト・プロセッサ向けに設計された包括的なソフトウェア・スタックによって補完されます2。
なお、ディスクリートのセキュア・エレメントを使用すれば、攻撃を受けたアプリケーション・プロセッサから別のICに保存された認証情報へのアクセスを防止することができます(隔離)。そのため、システムのレジリエンスが高まります。
セキュアなシステムを開発するためには、構造化されたアプローチを採用する必要があります。そのアプローチは、要件の収集、脅威のモデル化、セキュアな設計、実装、テスト、認証、保守を包含するものになります。セキュア開発ライフサイクル(SDLC:Secure Development Life Cycle)に従えば、開発プロセスに最初から確実にセキュリティ対策が組み込まれることになります。
ロボットのセキュリティを確保するための理想的なパートナー
アナログ・デバイセズ(ADI)は、セキュリティを確保するためのコプロセッサとして「MAXQ1065」や「DS28S60」といった製品を提供しており、ターンキー・ソリューションとなるICのベンダーといえます。しかし、ADIではそのようなICベンダーという枠組みを超えて、ロボット業界がセキュリティに関する多様な要件を満たせるような支援として、セキュリティとロボティクスに関する広範な専門技術の融合を図っています。それがロボットの安全を確保する上で直面する特有の課題に対処可能な理想的なソリューションを提供することにつながり、単なるICベンダーではなく、ソリューション・プロバイダとしての役割を担うことになるわけです。セキュリティやロボットに精通していることで、パートナーたちは包括的なソリューションの活用が可能となり、ハードウェア、ソフトウェア、システムの各レベルにわたる課題を解決できるようになるわけです。
また、ロボットのセキュリティを確保するためには、包括的なアプローチが必要だということを強く認識しています。それに基づき、コンポーネント・レベルの製品を開発するだけでなく、システム・レベルの視点で必要になるものを提供しています。つまり、ハードウェアとソフトウェアをカバーすることにとどまらず、システム間の通信やシステムの統合といった側面にも注目しています。それにより、すべての重要なコンポーネントをシームレスに統合できるようにしています。
ここで、ADIと自動車業界の企業による代表的なコラボレーションの例を紹介しておきましょう。それは、ワイヤレス・バッテリ管理(バッテリ・マネージメント)システム(wBMS:Wireless Battery Management System)に関するものです。ADIは自動車業界のパートナーと緊密な連携を構築することによってISO 21434の認証を取得したwBMSを開発しました。つまり、そのwBMSは安全かつセキュアなものであることが実証されており、堅牢性の高いセキュリティ対策を実現したことを示したこととなります。同時に、そのwBMSは包括的なソリューションを提供するというADIのコミットメントを具現化したものでもあります。
ADIは、セキュリティに関する実装を行うための自社保有の専門技術が広く活用されるようにしたいと考えています。そのためには、ロボット業界のパートナーとも、自動車業界で行ったのと同様の協調的な取り組みを推進する必要があります。ステークホルダと緊密に連携することにより、自動車分野での経験と成果を活かして安全かつセキュアなロボットの開発に貢献することが現在の目標の1つです。
また、セキュリティに関する多様な能力を活かすべく、献身的な取り組みを進めており、パートナーに対して、サイバーセキュリティに関連するあらゆる案件に対し、比類ないレベルの専門技術とサポートを提供しています。そのためシステム設計に携わる企業にとっての選択すべきパートナーとなれる素質を備えていると言えます。
ADIによるセキュリティの詳細な情報は、以下のようなアプローチによって取得することができます。
- EngineerZoneでは、セキュリティに関連するブログを公開しています。そこで行われるディスカッションに参加すれば、組み込みセキュリティのコミュニティとの交流を図り、知見を共有することができます。まずは質問するという形でコミュニティに参加することにより、進行中の議論に貢献していただければ幸いです。また、「セキュリティ」という語で検索を行えば、それに関する貴重な記事やリソースにアクセスできます。
- ADIのWebサイトの組み込みセキュリティのページや1-Wireに関するページを活用すれば、様々なセキュリティ製品に関する情報や貴重な知見を得ることができます。最新の技術記事、アプリケーション・ノート、ビデオを確認してもらうことで、セキュリティに関する理解を深めることができるでしょう。
- wBMSについては、ADIの無料の技術情報誌「アナログ・ダイアログ」の記事「ワイヤレス・バッテリ管理システムの新時代、注目すべきはセキュリティのレベル」が参考になります。
ロボットのジョイント・コントローラの構成例
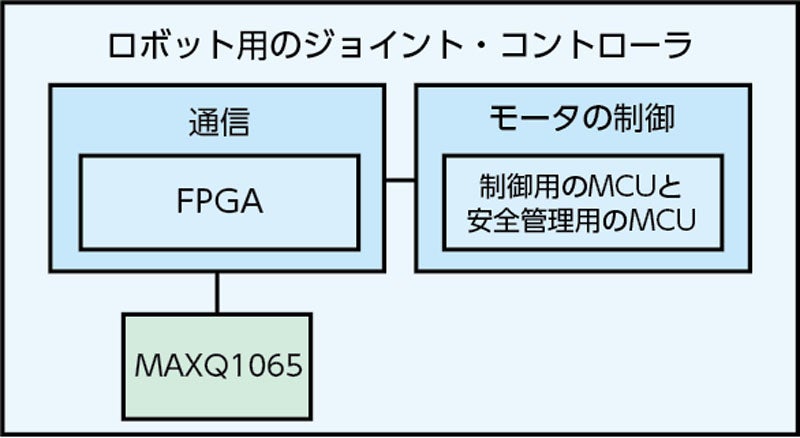
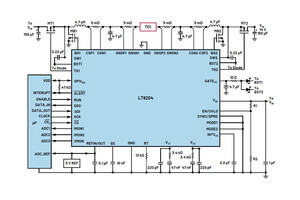
ロボットでは、ジョイント(関節)の制御が非常に重要です。図3に示したのは、ジョイント・コントローラの設計例です。
この設計では、MAXQ1065を採用しています。同ICを使用することにより、セキュア・ブートの機能を実装することができます。その結果、システム全体のセキュリティを強化することが可能になります。MAXQ1065は、暗号鍵用のセキュアなストレージ、セキュアな通信プロトコル、暗号処理などに対応する様々な機能を備えています。
まとめ
今後のロボット開発においては、サイバーセキュリティが非常に重要な要素になります。様々な脅威に対する保護を実現するには、セキュアな認証、暗号化された通信、サプライ・チェーンへのセキュリティ技術の適用といった強固な対策を導入することが不可欠です。重要なのは、サイバーセキュリティを何よりも優先することです。その上で、ADIの専門技術を活用すれば、相互に接続された世界に出現する新たなリスクを回避しつつ、ロボットの潜在能力を最大限に引き出すことが可能になります。
なお、「Robotic Security Use Cases and Implementation for a Secure Future(ロボットのセキュリティ機能のユース・ケースと実装、セキュアな未来を実現するには?)」というADIの記事では、サイバーセキュリティとロボットの関係について詳しく説明しているほか、現実のシナリオにおいてADIのセキュリティ製品を活用する方法も紹介しています。
本記事はAnalog Deviceの技術解説記事「Ensuring a Secure Future for Robotics: The Role of Cybersecurity」を翻訳したものとなります
参考資料
1:Jean-Paul A. Yaacoub、Hassan N. Noura、Ola Salman、Ali Chehab「Robotics Cyber Security: Vulnerabilities, Attacks, Countermeasures, and Recommendations(ロボティクスのサイバーセキュリティ -- 脆弱性、攻撃、対抗策、推奨事項)」International Journal of Information Security、2021年3月
2:Christophe Tremlet「IEC 62443シリーズの規格:サイバー攻撃からインフラストラクチャを保護する方法」Analog Devices、2023年4月