はじめに
先般、「ロボットのセキュアな未来に向けて、サイバーセキュリティが果たす役割」と題した記事にて、ロボットの制御を担うシステムが抱えるセキュリティ上のリスクについて説明したほか、ロボットを開発する際、産業分野向けのセキュリティ規格を遵守することの重要性を強調しました。また、ロボット制御システムの保護を強化する上で不可欠なセキュリティ機能についても解説しました。
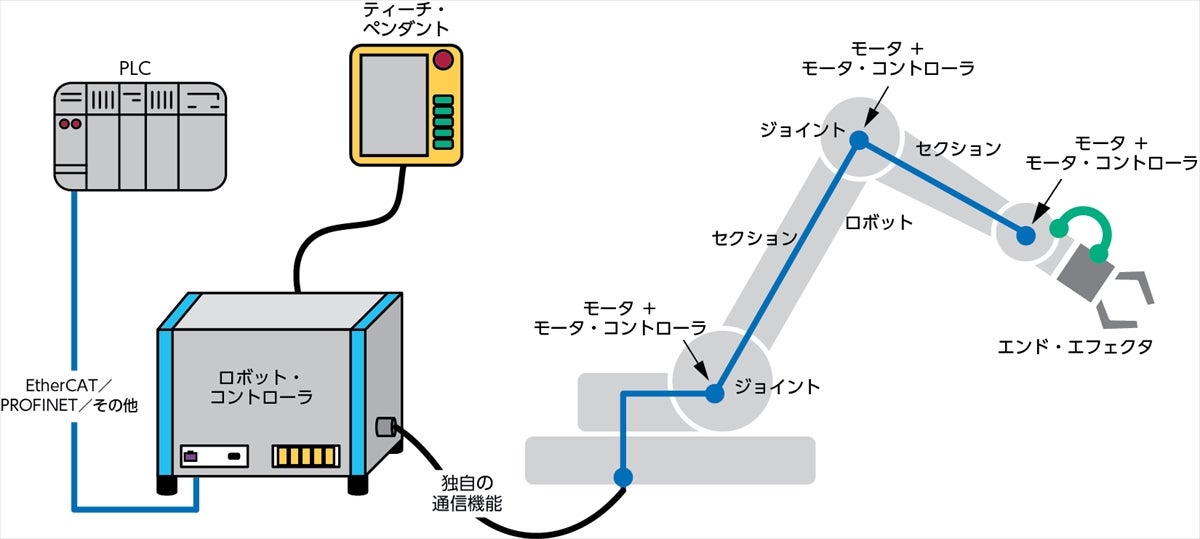
そうした取り組みを踏まえ本稿では、産業用のロボット/コボットの構成要素となる各種のコンポーネントについて説明します。注目すべきは、それらと似た多くのコンポーネントが、自律走行搬送ロボット(AMR:Autonomous Mobile Robot)やピック&プレース・システムでも一般的に使用されているということです。また、様々なロボットのセキュリティに関するユース・ケースについての検討を行った上で、セキュリティ向け半導体製品を活用することで、多様なロボット制御システムに必要な機能をどれだけシンプルに実装できるのかを考えていきたいと思います。
セキュアなロボット制御システムに必須の機能と開発アプローチ
ここでは、セキュアなロボット制御システムに必須の機能とその実装方法について説明します。まずは、本稿を読み進める上で前提となる知識について確認しておきましょう。必要になるのは、以下のような機能と実装方法です。
- セキュアな認証:デバイス/コンポーネントのIDを確認するためにセキュア認証用ICを採用する
- セキュアなコプロセッサ:セキュアなストレージと暗号化の処理に対応するための専用ハードウェアを活用する
- セキュアな通信:データ交換に対する保護を実現するために、暗号化用のプロトコルを実装する
- アクセス制御:システムに対する不正なアクセスを制限するために、権限をきめ細かく設定する
- 物理的なセキュリティ対策:物理的な改竄を防ぐための対策を導入する
セキュアなシステムを開発するためには、構造化されたアプローチを採用する必要があります。そのアプローチは、要件の収集、脅威のモデル化、セキュアな設計、実装、テスト、認証、保守を包含するものになります。SDLC(Secure Development Life Cycle)に従えば、開発プロセスに最初から確実にセキュリティ対策が組み込まれることになります。
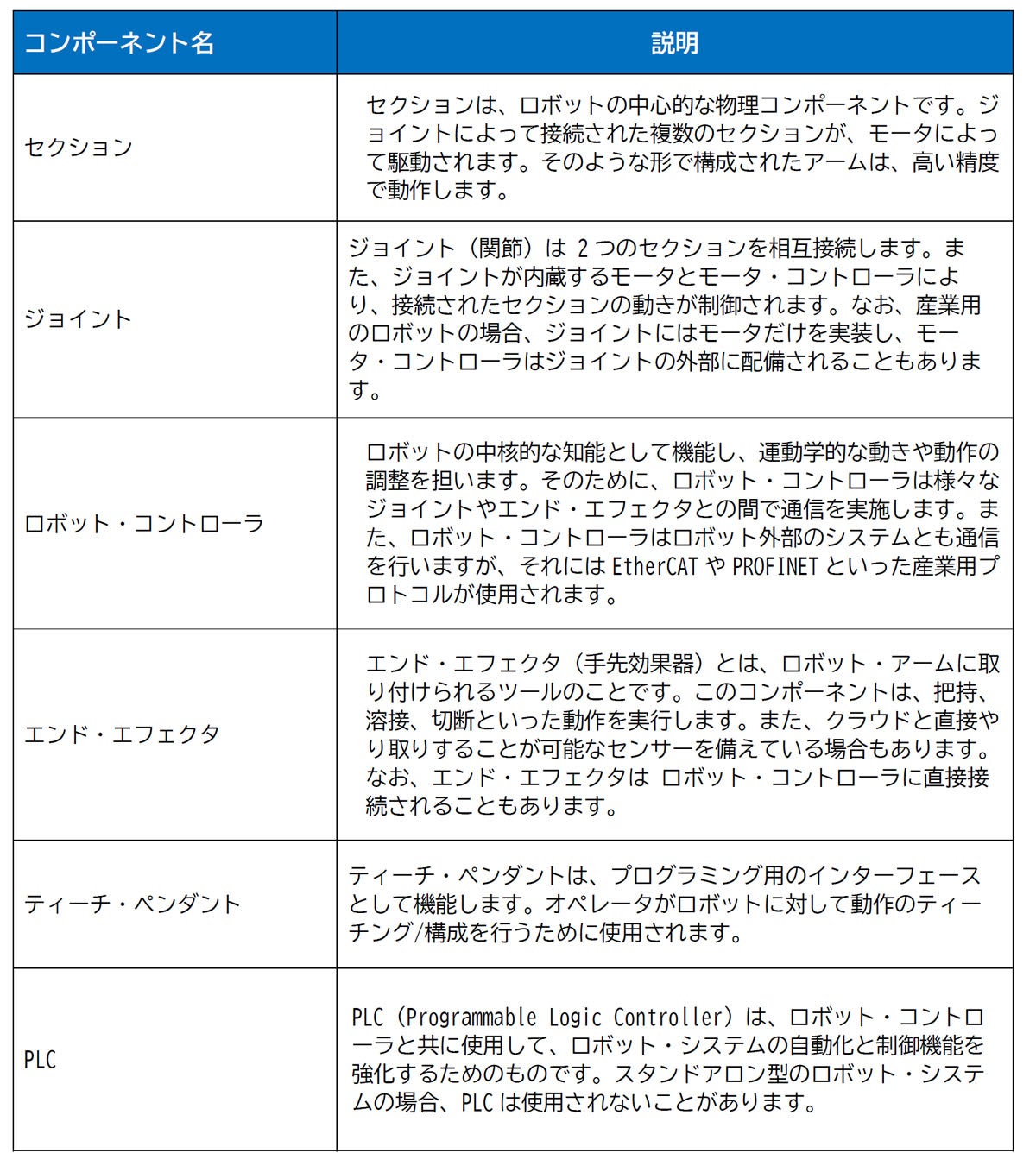
産業用のロボット/コボットの構成要素となるコンポーネント
図1は、産業用のロボット/コボットの構成要素となる一般的なコンポーネントを示したものです。また、表1にはそれらのコンポーネントの概要をまとめています。
ロボットのセキュリティ機能のユース・ケース
ここでは、ロボットに適用されるセキュリティ機能のユース・ケースについて説明します。その上で、アナログ・デバイセズ(ADI)が有する知識と製品を活用する形で設計/実装方法を考えてみます。
信頼性の高いPLCの動作、ゲートウェイの保護
PLCとロボット・コントローラを組み合わせることで、ファクトリ・オートメーション(FA)の環境における高精度の制御が可能になります。また、様々なプロセスをきめ細かく制御できるようになります。
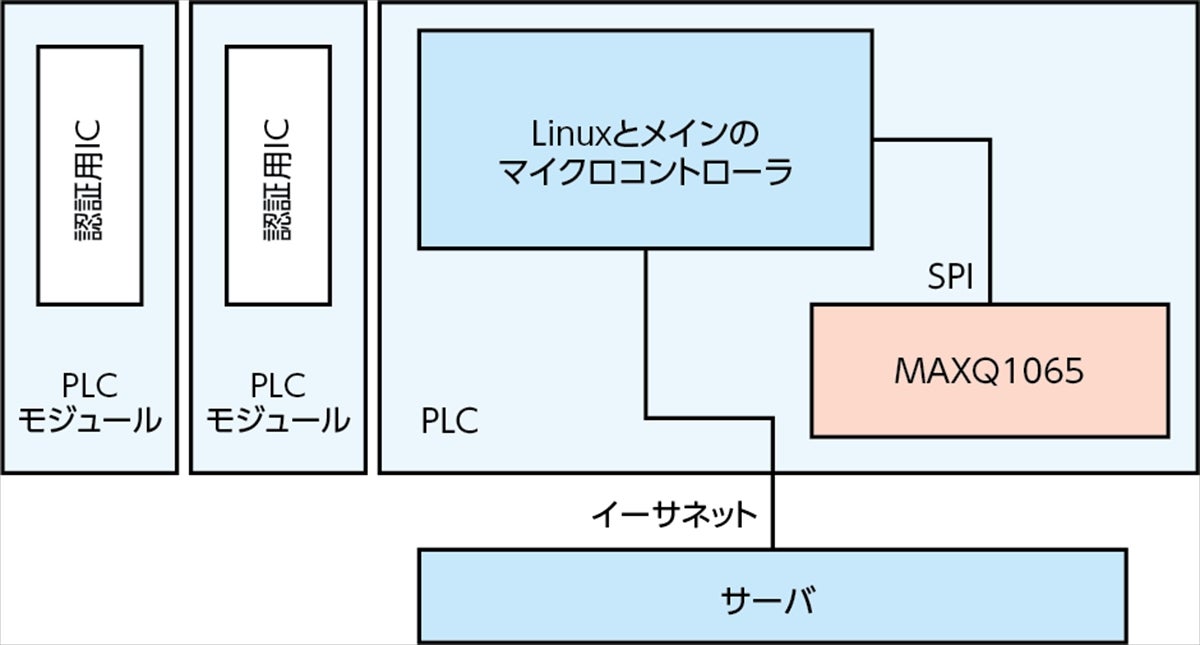
ロボットに関連する技術が進化した結果、PLCと同様の機能を備える統合コントローラが開発されるようになりました。FA環境における安全な運用を実現するためには、PLCの動作の信頼性とセキュリティを高めることが極めて重要です(図2)。
ADIでは、ChipDNA技術を適用した製品を提供することでセキュリティの向上を図っています。同技術は、個々の電子部品に固有の特性を利用してセキュアな暗号鍵を生成するというものです。その暗号鍵は、メモリには保存されません。また、セキュリティの侵害の対象になり得る静的な状態で保存されることもありません。そのため、サイバー攻撃に対する保護が強化されます。「MAXQ1065」は、このChipDNA技術を採用した暗号コントローラICで、組込機器向けの製品として、消費電力が少ないことを特徴とします。PLCにMAXQ1065のようなデバイスを適用すると、以下のようなユース・ケースをサポートすることが可能になります。
- PLCモジュールのセキュアな識別やクローニングの防止
- セキュア・ブート、ファームウェアのセキュアなダウンロード
- PLCモジュールとPLCサーバの間で行う非対称鍵による相互認証
- ECDH(Elliptic Curve Diffie-Hellman)鍵交換によるセキュアな通信セッションの確立
- ネットワークのパケットの暗号化/復号化に対するAES(Advanced Encryption Standard)の適用
ノードとクラウドの直接通信に対するセキュリティ
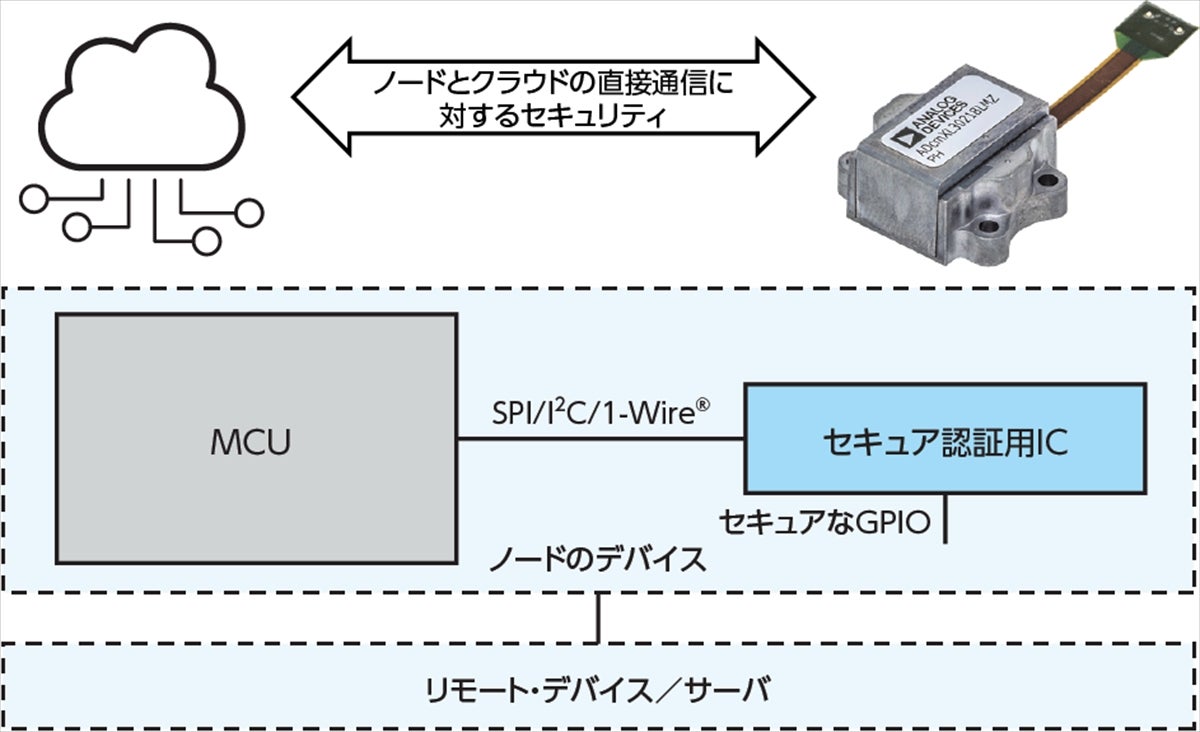
ロボットでは、ノードとクラウドの間で直接通信が行われることがあります(図3)。その場合、リモートでの監視、データの分析、ソフトウェアのアップデートといった様々な機能を実現できることになります。そのためには、両者の間の通信においてセキュリティを確保することが非常に重要です。
MAXQ1065を使用することで、センサーとクラウドの間、センサーとゲートウェイの間の通信に適用するセキュリティ機能を強化することができます。具体的には、以下のような効果が得られます。
- TLS(Transport Layer Security)プロトコルの実装が可能になり、暗号化されたデータのセキュアな送信が保証されます。TLSでは真正性が検証され、機密情報が保護されます。ノードとクラウドの間のセキュアな通信に不可欠な技術だと言えます。
- センサーとゲートウェイの間またはノードとゲートウェイの間で独自技術を用いた接続を行うことにより、セキュアな通信を容易に実現できます。コントローラは、鍵の交換とデータの暗号化を可能にします。それにより、通信チャンネルの保護が確立されます。また、RFベースまたはその他の独自プロトコルを使用する場合のセキュリティを強化することが可能です。
- ノードの認証、信頼性の高いノードの動作、セキュア・ブート、ファームウェアのセキュアなアップデートといったセキュリティ機能を追加できます。これらの機能により、ノードのアイデンティティを検証し、信頼できる動作を確保し、不正な改竄を防止することが可能になります。その結果、システムのセキュリティが強化されます。
センサーのデータの保護
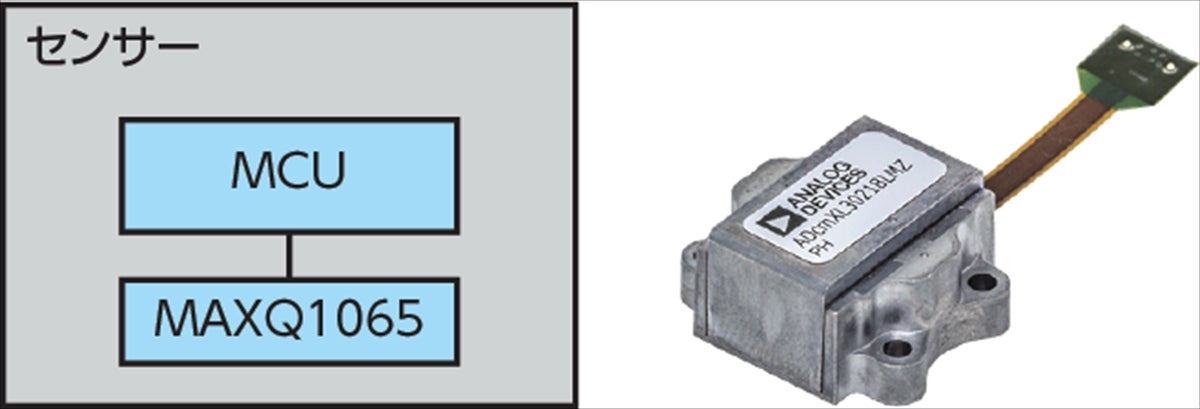
センサーで取得したデータについては、以下のような保護機能を適用できます。
- 保存されたデータにはChipDNA技術による暗号化を適用できます。
- センサーのキャリブレーションに使用する重要なデータやセンサーの構成情報は、MAXQ1065のセキュアなストレージ内に保存されます。それにより、改竄や漏洩を防止できます。また、暗号化を適用した上でシステム内に保存することも可能です(図4)。
サプライチェーンのセキュリティ
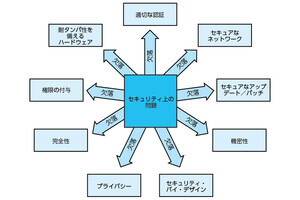
サプライチェーンのセキュリティには、様々なトピックが関連します(図5)。例えば、以下のようなことを実現する必要があります。
- 製品のクローン(偽造品)を防止する必要があります。
- IP(Intellectual Property)の喪失や収益の損失を防ぐためにはソフトウェア・ベースの機能を利用できます。それをイネーブルにする際のセキュリティを確保する必要があります。
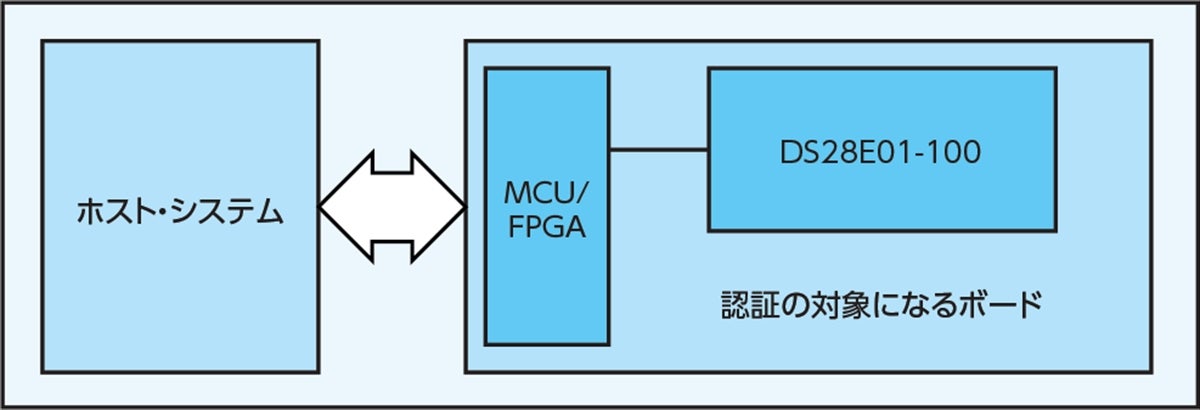
- ハードウェアの真正性を検証する必要があります(図6)。
以下のような理由から、サプライチェーンのセキュリティは、ADIのセキュア認証用ICを採用することで容易に確保できます。
- ADIが提供するプログラム済みの認証用ICは、高い堅牢性で偽造品からの保護を実現します。
- セキュアなライフサイクルの管理と鍵の管理により、デバイス/製品のライフサイクル全体にわたってアセットのセキュリティを維持できます。
- ADIの認証用ICを使用すれば、機能の有効化をセキュアに実行できます。それにより、貴重なIPを保護することが可能になります。
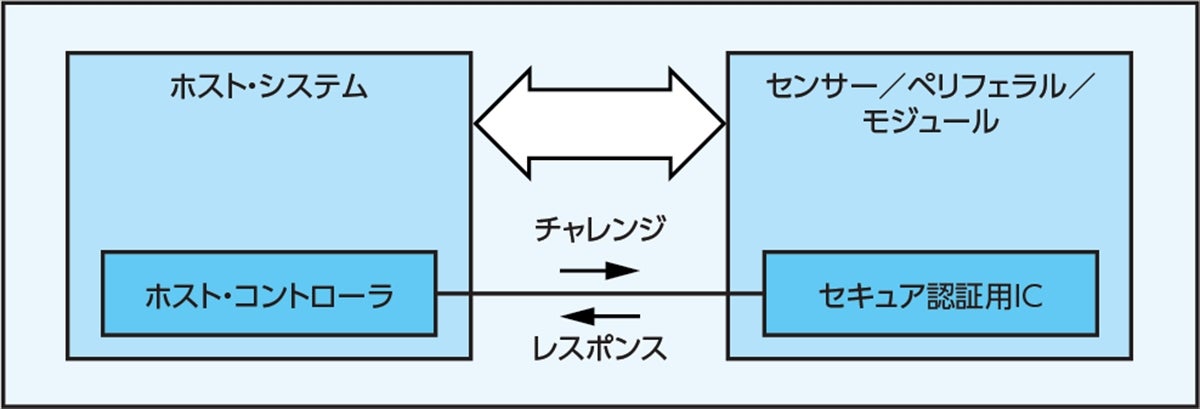
PLCとノードのセキュアな通信
セキュア認証用ICは、通信のセキュリティを確保することに役立ちます。対象になるのは、PLCとアクチュエータ/センサーの間の通信、PLCとSCADA(Supervisory Control and Data Acquisition)制御システム(SCADAのシステム内ではなくPLC内)の間の通信などです。セキュア認証用ICを使用すれば、TLSプロトコルがイネーブルになります。TLSは、インターネット・プロトコルをベースとした通信で広く使用されているトランスポート層用のセキュアなプロトコルです。
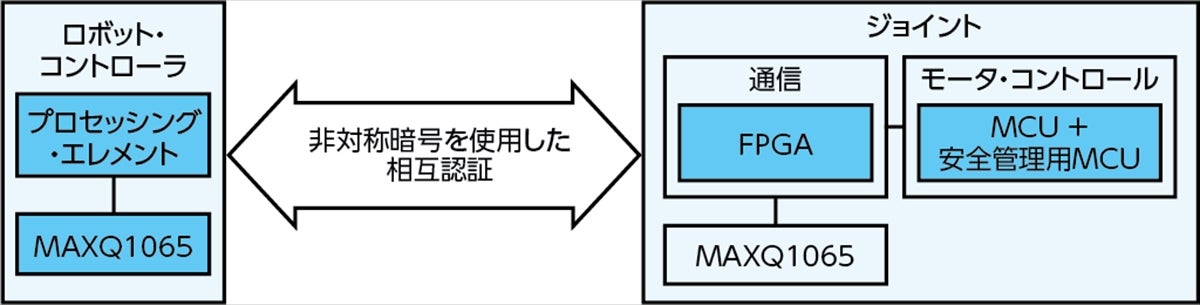
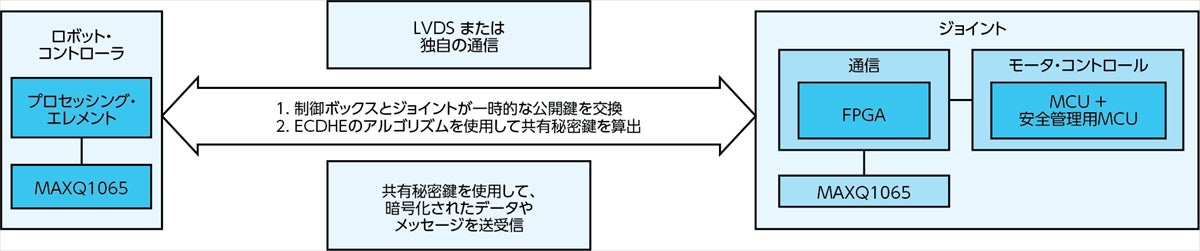
ロボットのジョイントの認証
図7は、ロボットにジョイントの認証機能を実装する方法を示したものです。これにより、ロボット・システムの内部では、正当かつ認証済みのエンティティだけしか、やり取りに加われなくなります。その結果、全般的なセキュリティが強化されます。より詳しく言えば、不正アクセスを効果的に防止したり、通信のセキュリティを強化したりすることが可能になります。このことは、システム全体の完全性と信頼性の確保に役立ちます。
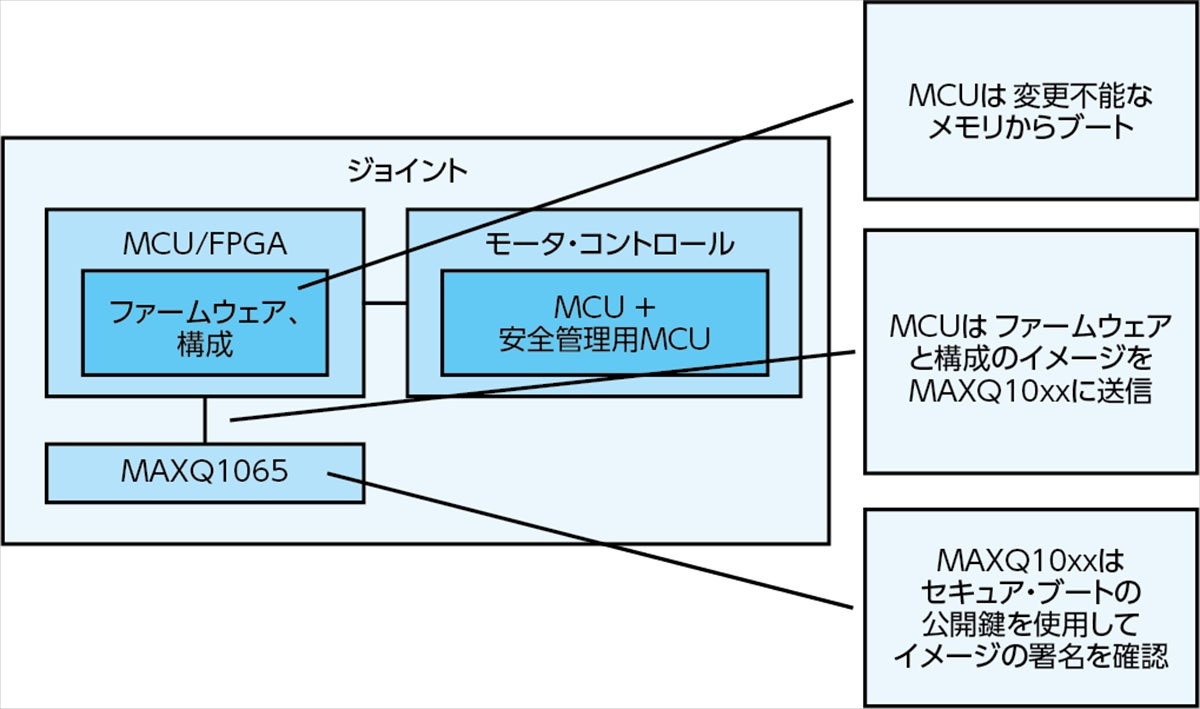
ジョイントのセキュア・ブート
ロボットのジョイントのセキュア・ブートは、図8のようにすることで実現できます。セキュア・ブートは、セキュアで信頼できる動作環境を構築するための強固な基盤になります。具体的には、不正なソフトウェアの実行、マルウェア、改竄に対する保護を実現し、システムのセキュリティと信頼性を強化する役割を果たします。重要なのは、チェーン・オブ・トラスト(Chain of Trust)を確立し、ソフトウェア・コンポーネントの完全性を検証することです。その結果、ジョイントのセキュア・ブートによって、ロボット・システムの動作全体の完全性と真正性が確保されます。ジョイントのセキュア・アップデートも同様の方法で実現されます。
ジョイント/ロボット・コントローラにおける機能の選択的な有効化
セキュア・ブートに成功したら、アプリケーションのマイクロコントローラ(MCU)/プロセッサ/FPGAは、認証用IC/コプロセッサのセキュアかつ構成可能なメモリからデータを読み出します。それにより、ジョイントまたはロボット・コントローラの機能を選択的に有効にすることができます(図9)
キャリブレーション・データ用のストレージ
ペリフェラルの中には、工場から出荷される際、個別にキャリブレーションされるものがあります。それに向けた高精度の測定を維持するためには、キャリブレーション・データ用のストレージが不可欠です。同データを認証用IC内にセキュアに保存することにより、完全性を確保し、不正なアクセスからの保護を実現することが可能になります。
ホスト・システムは、保存されたデータを読み出したり、利用したりすることが可能です。つまり、ペリフェラルから精度と信頼性に優れる測定値を取得することができます。キャリブレーション・データ用のセキュアなストレージにより、システム全体の精度と性能が向上します。また、貴重な知見が得られ、高い品質基準を維持することが可能になります。
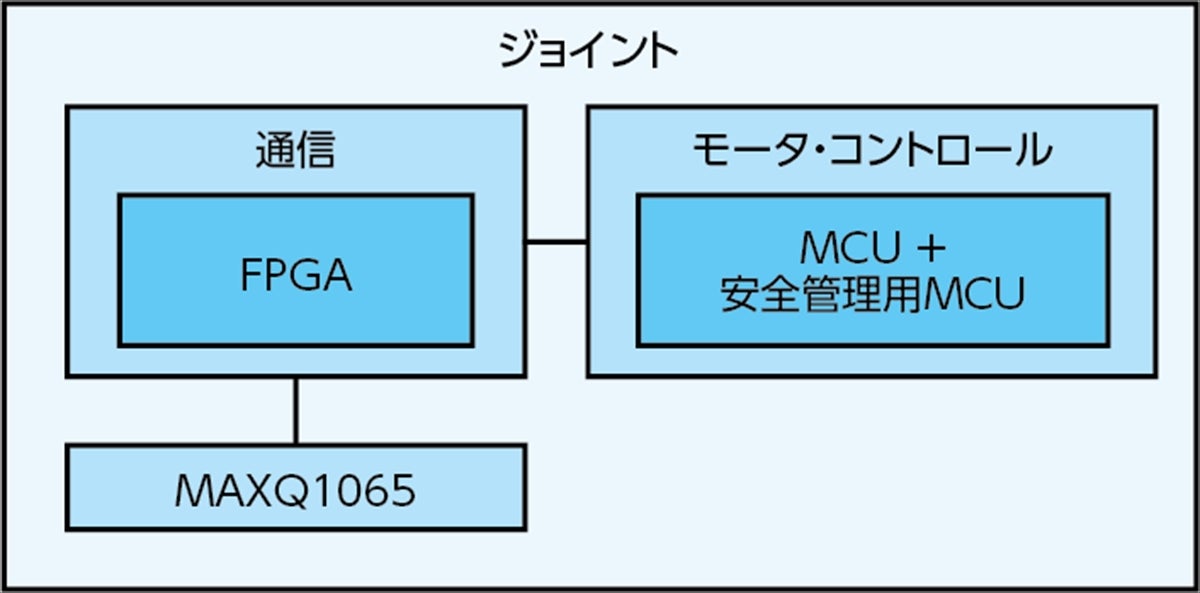
ジョイントとのセキュアな通信
ジョイントとのセキュアな通信を実現することにより、ロボット・システム全体のセキュリティ体制が強化されます。また、信頼性が高く保護されたデータ交換を実現可能になります(図10)。
まとめ
ロボットの未来をセキュアなものにするためには、サイバーセキュリティが非常に重要です。脅威からの保護を実現するには、セキュアな認証、暗号化を利用した通信、サプライチェーンのセキュリティといった堅牢性の高い対策が不可欠です。ADIの製品/ソリューションを採用することでも高度なセキュリティ機能を利用することができるようになり、ロボット・システムの完全性と信頼性を確保することが可能になります。重要なのは、サイバーセキュリティを何よりも優先することです。その上で、ADIが提供するような専門技術を活用すれば、相互に接続された世界に出現する新たなリスクを回避しつつ、ロボットの潜在能力を最大限に引き出すことが可能になります。
本記事はAnalog Deviceの技術解説記事「Robotic Security Use Cases and Implementation for a Secure Future」を翻訳したものとなります
参考資料
・Jean-Paul A. Yaacoub、Hassan N. Noura、Ola Salman、Ali Chehab「Robotics Cyber Security: Vulnerabilities, Attacks, Countermeasures, and Recommendations(ロボティクスのサイバーセキュリティ -- 脆弱性、攻撃、対抗策、推奨事項)」 International Journal of Information Security、2021年3月
・Christophe Tremlet「IEC 62443シリーズの規格:サイバー攻撃からインフラストラクチャを保護する方法」Analog Devices、2023年4月
・「セキュア認証によるR&D投資の保護」Analog Devices
・「The Basics of Using the DS28S60(DS28S60の基本的な使い方)」Analog Devices